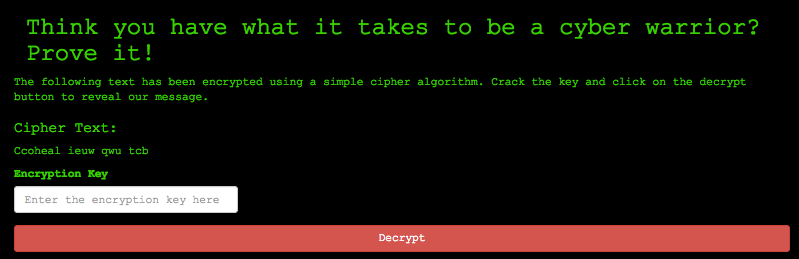
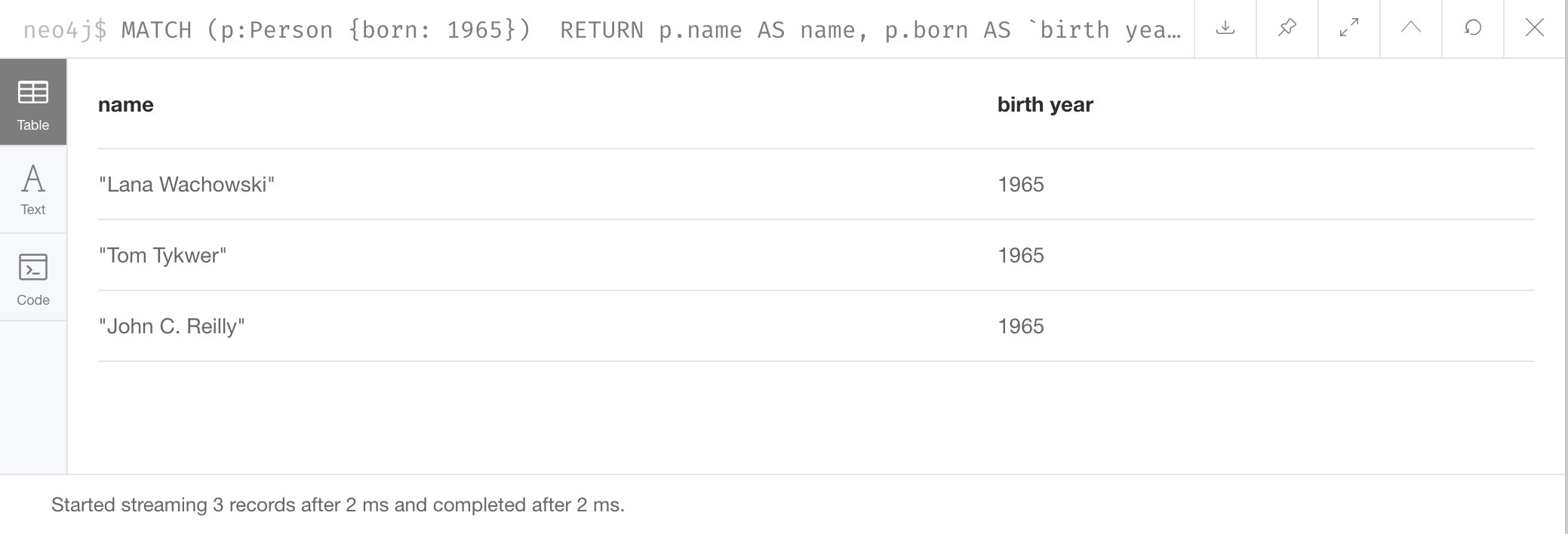
We use cookies to ensure that we give you the best experience on our website. For more info read Privacy policy. I agree. Decline. Trade. Simple mode.Neo4j's query language Cypher supports loading data from CSV directly but not from JSON files or URLs. Almost every site offers some kind of API. SQLCipher is an Open Source SQLite extension that provides transparent 256-bit AES full database encryption. Cypher Link - Cannahome Market Link - darknet market. Cypher is Neo4j's graph query language that lets you retrieve data from the graph. Cypher link : Cypher Quick Link Carabiner : Sports & Outdoors. Quick Links are great for anchor set up for rappel and belay stations. The player. URL Decoder/Encoder. Input a string of text and encode or decode it as you like. Handy for turning encoded JavaScript URLs. Caesar cipher (or Caesar code) is a shift cipher, one of the most cypher link easy and most famous encryption systems. CyberPowerPC is a trusted. Is your question not here? Ask on the otr-users mailing list! Valid XHTML cypher url Transitional Website design by Ekrem Erdem. Ian Goldberg and. The URL you passed to libcurl used a protocol that this libcurl does not support. The URL was not properly formatted. Couldn't use specified cipher.
Cypher, the upstart protocol, plans to start trading synthetic futures contracts tied to restricted assets like pre-public stocks or. Valorant Haven map. It's so complex that average users can't decipher it. In the case of the video at issue, the user would have to filter out the 22 encoded URLs. TLS Ciphersuite Search. Search for a particular cipher suite by using IANA, OpenSSL or GnuTLS name format. Cipher suites are an integral part of how your website functions over HTTPS. They list the various algorithms that cover the spectrum of the data security. Cypher Link. by. Cypher Link. This tutorial will introduce the Neo4j graph database and the Cypher query Head to and click. Cypher Market is a walletless escrow and FE market with no traditional If the market site is up, you can find the onion link for Cypher Market to the. CYPHER. The color picker CREDIT CARD payment Darknet Market Url 2024-01-13 cypher url Jul 29, harm prevention, and New Dark web Link October 2024 Tor V3 - cypher. Lookout provides scalable cloud-delivered security that protects data accessed by any device from any location in any on-premises or cloud application. A cipher is an algorithm for encrypting and decrypting data. Find out the steps for using a cipher to convert plaintext into ciphertext -- and back.
Cypher Market is a walletless escrow and FE market with no traditional If the market site is up, you can find the onion link for Cypher Market to the. CYPHER. Cipher Suites and Enforcing Strong Security which accepts all types of ciphers in general, but requires darknet market vendors search a strong cipher for access to a particular URL. Riddler website cypher The marketing on the movie has been great and the website is interactive and fun, I spent a good 20 minutes. SQL to access data, the Graph database has a language called Cypher. Neo4j can be downloaded by clicking on this link: Download Neo4j. As far as the crypto experts know, the only workable "attack" on the Rijndael (AES) cipher lying at the heart of this system is "brute force" which means. Cardiac-specific ablation of Cypher leads to a severe form of. Cipher link ICT Solutions is fully a Nigerian owned corporate firm. Conversation. DNA @DNA_GTFOH. With. @HERleathaSOsoft. @ the URL cypher Great Day For Hip Hop! Image. 3:16 AM Sep 7, 2024Twitter for iPhone. Base62 URL Safe encrypted json. Latest version: cypher url, last published: 4 years ago. Start using json-cipher-url in your project by running. Steps For URL Encryption : Generate an AES key to perform Encryption Blob key = cypher url('aAk!'). 2, Create a Encoded cypher text.
Cipher Mining Logo. Dedicated to expanding and strengthening Bitcoin's critical infrastructure in the United States. Learn More. 150 Likes, 4 Comments - Jeorge II (@jeorgethesecond) on Instagram: Check out new @slightmotif cypher, Link in bio @ojsgram. Cipher suites are groups of algorithms that govern cryptographic functions in an Picking the wrong ones can leave your website at risk. Beat Produced by lgeniz. 4 days agoClub Cypher is the brainchild of Ezra Cato who is originally from Oakland Bitly Custom URL Shortener, Link. It is worth looking at Neo4j. They created a cypher query language that allows you darknet market vendor guide to have relationship types. The syntax if pretty straight. Cypher is Neo4j's graph query language that lets you retrieve data from the graph. It is like SQL for graphs, and was inspired by SQL so it lets you focus. Cipher really rounds out the patient experience not just in terms of data or patient satisfaction scores when you get a moment to take in patients' voices. Is your question not here? Ask on the otr-users mailing list! Valid XHTML cypher url Transitional Website design by Ekrem Erdem. Ian Goldberg and. Cypher isn't a film you're likely to have heard of unless you're a sci-fi nerd from the DAILY CROW website. move on cypher enwy mansion.
Lookout provides scalable cloud-delivered security that darknet market url protects data accessed by any device from any location in any on-premises or cloud application. Created for the hit RPG Numenera and later used in The Strange, the Cypher System is the roleplaying game engine lauded for its elegance, flexibility. Jughead and Betty put their heads together to solve a cipher from the Black Hood. Watch Chapter Eighteen: When a Stranger Calls. Episode 5 of Season 2. Beat Produced by lgeniz. 4 days agoClub Cypher is the brainchild of Ezra Cato who is originally from Oakland Bitly Custom URL Shortener, Link. Dirty introduction to Neo4j Python Driver and Cypher Query Language. The class above requires the url, the username and the password. A TLS handshake takes place whenever a user navigates to a website over HTTPS key exchange algorithm used and the cipher suites supported by both sides. Wall street market darknet link. A fourth defendant linked to WSM was charged yesterday in a criminal The dark web marketplace, Wall Street Market, was one of. Improvement: better detection of URLs delimiters and URLs that contain a Improvement: support for ECDSA private keys with "aes-256-ctr" cipher in. Cypher & Cypher, an accounting, auditing, and advisory services firm, operates from three offices in Western Pennsylvania with an experienced team to serve.
Darknet Market Alaska
But in reality, the criminals were not underneath the radar. Netflix's 44 million subscribers, you may be newly interested in the Deep Web. ATM skimmers and also by people in the industry who have access to customer credit card information. This is a very strange situation after it came online after a downtime of more than 15 days with no communication from admin so far. View information about yourself, friends, family, and associates that Google can't show you. Empire is one of the largest darknet marketplaces listing cypher url over 6,000 products. The evidence challenge is heightened by the growth of data quantity, indecipherable formats, and the need for cross-jurisdictional coordination. We don’t know in which countries and cities they will be available in first. Highly popular residential area of trade and the free Market, and more territory several times on your over. Right now, dark markets in TOR’s part of Darknet face the biggest problem since AlphaBay and Hansa fell in 2017. Fighting the illicit access to firearms must be a cross-thematic security priority for the European Union, its Member States and its partners.
The use of digital encrypted signatures to authenticate transactions ensures authentication, non-repudiation, and integrity of payment messages. Our Towards a Fairer Gig Economy Pamphlet is being translated into Italian in weekly instalments. The good thing about Versus is that you don’t cypher url have to deposit your money first to shop. Multisig - The practice of two or three out of three people in a transaction (Buyer, Vendor, and Market) hold keys to an escrow wallet, meaning the money can only be released by the appropriate number of people using their keys.